USPTO Allows More Prioritized Patent Applications To Be Filed
Takeaway: The USPTO is raising the number of allowed Track One program patent applications from 12,000 annually to 15,000 to expedite patent handling.

The U.S. Patent and Trademark Office’s Track One program allows inventors and companies to request their patent applications be expedited, for a fee of $4,000. This program started in 2011 and allows inventors to have their application examined within an average of eight months, as opposed to 24 months for a normal application.
Previously, 12,000 Track One applications were processed annually. The USPTO is increasing the number to 15,000 a year.
The USPTO states that “the number of requests for prioritized examination has been increasing steadily over the years.” In fact, in 2019, they increased the number from 10,000 to 12,000 a year.
Track One applications are only a fraction of the U.S. applications filed. In total, the USPTO examines approximately 640,000 applications and requests for continued examination per fiscal year.
Photo Credit: uspto .gov/ patents/initiatives/usptos-prioritized-patent-examination-program
Disney Wins Toy Story 4 Trademark Suit Against Evel Knievel Brand Owner
Takeaway: Disney character Duke Caboom is found not to be infringing on Evel Knievel, after it passed the two-pronged test set out in Rogers v. Grimaldi.
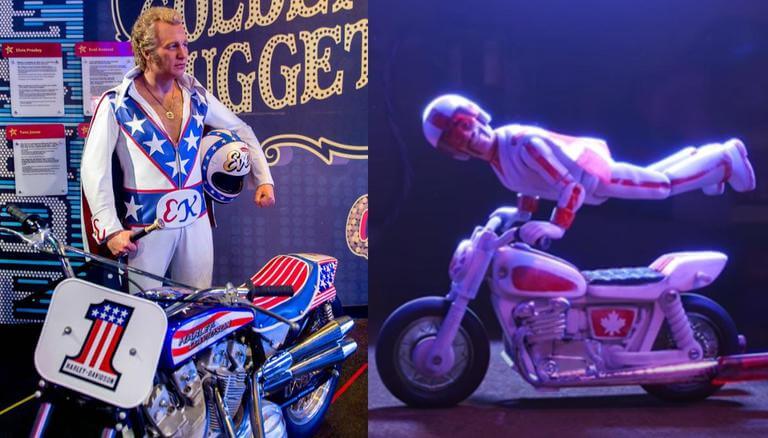
Disney’s hit movie “Toy Story 4” depicted its character Duke Caboom as a toy version of a Canadian motorcycle daredevil. K&K alleged that the Disney character, who was voiced by the actor Keanu Reeves, was confusingly similar to American stunt performer Evel Knievel. Specifically, they alleged that there would be confusion due to the similarly in his stunts, jumpsuit, commercials, etc.
According to a Nevada district court, there was not enough evidence to find that Disney intentionally misled consumers into believing its Duke Caboom character was connected to Knievel. Judge Mahan found that Disney’s use of Knievel’s likeness contains significant transformative elements. Further, the claims that Disney violated K&K’s right to publicity were also dismissed.
Duke Caboom’s role in the film passed the two-pronged test set out in the case Rogers v. Grimaldi. This test is applied to expressive works to balance potential trademark infringement with First Amendment rights. A claim against an expressive work outweighs a First Amendment defense when it a) has some artistic relevance to the underlying work and b) is used to explicitly mislead consumers.
The district court concluded that Disney met the low standard (“merely above zero”) for proving that the alleged allusion to Knievel had artistic relevance to the movie.
Photo Credit: www. republicworld .com /entertainment-news/hollywood-news/toy-story-4-makers-dragged-to-court-for-character-resemblance.html
USPTO Opens Pool of Possible Patent Examination Applicants To Become Patent Attorneys and Patent Agents
Takeaway: The USPTO finalizes rules of those who can take the patent bar examination and practice before the U.S. Patent Office, specifically by expanding the list of accepted degrees or additional necessary training requirements.
The U.S. Patent and Trademark Office released a notice that it is going to open up the pool of who is qualified to take the U.S. patent exam.
An examination applicant has to meet one of three criteria categories: Category A was for applicants with specific computer science, engineering, science or technology bachelor’s degrees; Category B was for those with a combination of another bachelor’s degree and additional training, such as 24 course hours of physic or 30 course hours of chemistry; and Category C included those with certain practical experience, such as passing the Fundamentals of Engineering test.
The opening of the applicant pool will add a new list of degrees to Category A that are currently part of Category B. Those degrees include aerospace engineering, bioengineering, biological science, biophysics, electronics engineering, genetic engineering, genetics, marine engineering, materials engineering, materials science, neuroscience, ocean engineering and textile engineering.
Additionally, the agency is making a change to allow advanced degrees in Category A to qualify under that category and would adjust how core sciences could be combined under Category B to qualify those applicants for the exam.
Emerging Cyber Threats To Be Aware Of
Takeaway: Sophisticated cybercriminals are constantly finding new ways to exploit users and steal sensitive information, thus additional protection steps are needed.

Karim Hijazi, CEO of cyber intelligence company Prevailion, cautions U.S. citizens of the five emerging threats to be aware of today, including what he refers to as “wipers,” “evil AI,” “firmware attacks,” “supply chain hell,” and “5G+ and space-based internet.”
Wipers
Wipers are a type of destructive malware that permanently deletes data rather than attempts to extort the victim. Hijazi cautions that although wipers are not frequently used, several national governments have increasingly been using this technique against foreign nations, and individual hackers could adopt similar measures.
Artificial Intelligence
Hijazi cautions about the use of AI, specifically the use of deepfake videos, also known as videos that impersonate a person. Victims are often prominent government leaders, CEOs, and celebrities. In general, AI is also increasingly being used to launch phishing attacks.
Firmware Attacks
Firmware is the code that runs behind an operating system. Hijazi says, “Hackers are figuring out how to target ‘firmware’ with malware in order to gain God-level access to these devices and even physically sabotage them.” This is especially dangerous because if a hacker obtains access to firmware, they will essentially control an entire device.
Supply Chains
Supply chain attacks are relatively new but have already been the subject of discussions due to several recent high-profile data breach cases. This type of attack seeks to infiltrate and disrupt the computer systems of a business supply chain. Several nation-states have already began practicing this type of cyber-attack.
5G and Space-Based Internet
Hijazi notes that as internet connectivity develops, cybercriminals will learn to exploit new vulnerabilities. In the upcoming years, you can expect to see a wide range of attacks on botnets, an increase in massive data theft, and much more.
Consult with your Cyber Security Experts to see if these additional threats are being addressed, and develop internal protocols to protect your data against these threats.
The Weeknd is Being Sued for Copyright Infringement Over Hit Song
Takeaway: Musical Artist The Weeknd is being accused by two music producers claiming that “Call Out My Name” infringes their song.
The Weeknd, who performed in the 2021 Superbowl Halftime Show, is being accused of copyright infringement by two music producers. The music producers claim that the Weeknd’s hit song, “Call Out My Name,” infringes the producers song “Vibeking,” as it contains many specific elements similar to their song.
The producers also claim to have sent a member of the Weeknd’s team “Vibeking,” and the Weeknd even commented on the song stating that “it’s fire.” In addition to the Weeknd, Universal Music Group as well as Sony Music Publishing are named among the defendants in the recently filed case in the Central District of California.
Defendant Instagram Wins Copyright Suit Regarding Embedding Posts From Their Online Platform
Takeaway: CA judge rules that Instagram cannot be a secondary infringer because third parties embedding Instagram posts on their websites are not liable for copyright infringement.

A group of photographers sued Instagram claiming that its embedding tool enables users to infringe their copyrights. A California judge ruled that Instagram could not be a secondary infringer where third parties embedding Instagram posts are not direct infringers.
In applying the “server test,” the judge reasoned that because websites do not “display” a copyrighted image, if it is not stored on the third parties original website and merely embedded in search results, no direct infringement takes place. With that being said, there can be no secondary infringement if there is no direct infringement, thus Instagram is off the hook.
Cislo & Thomas LLP Spotlight
C. Wook Pak, Esq. | Ph.D. and Patent Expert

As Partner and Chair of the Patent Prosecution Department at Cislo & Thomas, Dr. Wook Pak helps implement systems and procedures for the firm to efficiently and effectively procure patents for clients, among other matters. Also, as an IP litigator, he helps his clients enforce their intellectual property rights as well as defending against false allegations of infringement.
Dr. Pak’s early interest in patent law started when he wrote and filed a patent application for his own invention. This initial experience gave him a passion for guiding his clients to achieving their intellectual property goals.
Prior to being a patent attorney, he obtained a B.S. in biochemistry and biophysics and a Ph.D. in Neuroscience. In his over 15 years at Cislo & Thomas, he has assisted clients in procuring and enforcing their intellectual property rights in all fields, from medical devices, pharmaceuticals, and biotechnology to consumer products and business methods.
When Dr. Pak isn’t helping clients achieve their IP dreams, he enjoys spending time traveling with his family and practicing martial arts.
Enjoy keeping up with IP news?



